In early 2024, a multinational firm made global headlines for a $25 million disaster. It didn’t happen because of a server room fire or a masked hacker. It happened because an employee joined a video conference with his “CFO” and five “colleagues.”
They looked real. They sounded real. They even referenced private company jokes. But every single person on that screen was a sophisticated AI deepfake. By the time the call ended, $25 million was gone forever.
The Identity Crisis of 2026
In the Las Vegas entertainment and hospitality industry, we rely on “Big Name” trust. We trust the voice on the radio, the face on the Zoom call, and the credentials of the person entering the server room.
But as we head into March 2026, Identity-Led Sabotage has officially invalidated the old rules of security.
The Harm: Beyond the Bank Account
When a “Phantom Executive” strikes, the harm isn’t just financial. It is a total collapse of internal trust.
- Operational Paralysis: If you can’t trust an email from your CEO, how do you move projects forward?
- Brand Invalidation: For a resort or casino, a breach like this suggests your guests’ private data is just as vulnerable as your corporate treasury.
- The Two Opposing Forces: You are caught between The Speed of Business (needing to move fast) and The Precision of Security (needing to verify everything).
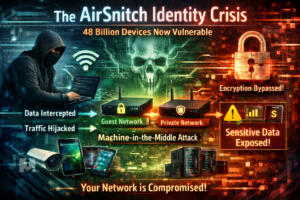
Why Traditional MFA is Failing
The most controversial truth in tech right now? Traditional 2FA (text message codes) is dead. Hackers are now using “Social-Engineering-as-a-Service” platforms that automate the process of tricking employees into handing over codes. If your security relies on a “point-in-time” check, you are leaving the door unlocked for the “Body Snatchers” of the digital age.
Why Partner with Get Custom Tech? The Seasoned Hand in a Modern Fight
This is not a theoretical scenario. This is the reality of 2026. And the time for theorizing is over.
Most technology firms approach security as a cost center, a checklist, or a piece of software to be resold. Get Custom Tech approaches it differently.
We are battlefield-tested engineering partners.
Depth, Not Breadth
We don’t chase every tech trend. Since 1995, we have specialized exclusively in complex Enterprise Identity Governance and Operational Technology (OT) security. We don’t sell antivirus or Wi-Fi systems. We solve one singular, critical problem: Is the entity requesting access who they say they are?
The “White-Glove” Mentality
We understand that a security solution that stops your team from working is just as dangerous as a successful hack. Our partners include:
- Veteran Systems Architects: Your primary contact isn’t a junior account manager; it’s an engineer who has spent decades building, breaking, and securing high-availability environments.
- Ex-Regulatory Compliance Specialists: We understand the complex interplay between Nevada Gaming Commission regulations and modern technical constraints.
The Get Custom Tech Standard: Continuous Resilience
We don’t just “install security.” We build Resilient Identity Ecosystems designed for the 24/7 reality of Las Vegas. Our approach is based on engineering principles, not marketing slogans.
- Identity Liveness: Beyond the Face We don’t just use facial recognition. Our stack utilizes advanced, real-time “liveness checks”—including spectrum audio analysis and retinal reflectance—to identify the signature “digital imperfections” inherent in synthetic media, ensuring the person on the other end is truly made of flesh and blood.
- Continuous, Non-Intrusive Authentication A login is only valid for milliseconds. We deploy Passive Biometrics(e.g., verifying gait, typing cadence, and mouse movement). If an authorized user’s unique “behavioral signature” suddenly shifts, the session automatically terminates and flags security.
- The “Vegas Protocol”: Physical Out-of-Band Verification For high-risk actions (such as wire transfers, administrative changes, or accessing high-limit gaming data), we implement a physical, air-gapped verification process. Even if the CEO has been perfectly simulated on Zoom, the system requires a secondary, physically present biometric confirmation to proceed. We build friction where it must exist.
Trust is Earned in the Dark
Most tech companies tell you what they can do. We tell you what the threats are actually doing. We believe that trust isn’t built with a sales pitch; it’s built with Transparency and Readiness.
When the stability of your corporate treasury and the confidence of your guests are at stake, you need a partner who can see in the dark.
Is the person on your next video call who they say they are? Let’s make sure of it.
Schedule an Identity Vulnerability Audit with a Lead Get Custom Tech Engineer today.
Call or Text now at 702-209-0252!